Scams are no longer rare events that only affect a few unlucky individuals. They have become part of everyday life in both digital and real world environments. As technology advances and online platforms grow, scammers adapt quickly and refine their tactics to appear more believable and more personal. Many scams today look professional, sound convincing, and are designed to exploit trust, urgency, and fear. Even highly educated and tech savvy individuals can fall victim when caught off guard or emotionally pressured.
What makes scams particularly dangerous is how subtle they can be. Some arrive as simple emails that look exactly like official messages from banks, delivery companies, or government offices. Others come through social media messages, phone calls, or even job listings that seem legitimate at first glance. Scammers rely on the assumption that most people are busy and will not take time to verify details. A single click, reply, or shared piece of information can be enough to trigger serious financial loss or identity theft.
Offline scams continue to be just as damaging. Fake charity collectors, impersonators, and fraudulent investment promoters still operate through phone calls, printed letters, and face to face interactions. In times of crisis or economic uncertainty, these scams often increase, targeting people who are seeking help, income, or hope. The emotional impact can be just as severe as the financial damage, leaving victims feeling embarrassed, violated, or powerless.
Understanding how common scams work is one of the strongest defenses available. Awareness does not require advanced technical knowledge, only a willingness to pause, question, and verify before taking action. This list breaks down ten of the most common scams affecting people today, explaining how they operate, why they work, and what warning signs to watch for. Staying informed helps protect not only yourself, but also your family, friends, and community. Knowledge remains one of the most effective tools against fraud, both online and offline.
1. Phishing Emails and Fake Websites
Phishing emails and fake websites are among the most common and effective scams because they imitate trusted institutions people interact with every day. These scams typically arrive through email, text messages, or messaging apps and appear to come from banks, online retailers, delivery services, payment platforms, or government agencies. The message often claims there is an urgent issue that requires immediate action.
Common examples include warnings about suspicious account activity, failed deliveries, password resets, or payment problems. The message usually includes a link that leads to a fake website designed to closely resemble the real one. Logos, layouts, and even web addresses are carefully crafted to look authentic. Once on the site, victims are prompted to enter login credentials, personal information, or financial details.
Modern phishing scams are highly polished. Many contain no spelling or grammar errors and use real branding elements. Some messages are personalized using information obtained from previous data breaches or public profiles. This makes the scam feel legitimate and targeted rather than random.
Once information is submitted, scammers can access accounts, transfer funds, make purchases, or commit identity fraud. In some cases, the stolen information is sold to other criminals, leading to long term consequences for the victim.
The best protection is caution and verification. Avoid clicking links in unexpected messages, even if they appear urgent. Instead, visit official websites by typing the address directly into your browser. Check sender addresses carefully and be wary of messages that pressure you to act quickly. Legitimate organizations rarely ask for sensitive information through unsolicited messages.
Image

2. Tech Support Scams
Tech support scams exploit fear and unfamiliarity with technology. These scams often begin with a sudden popup message on a computer screen claiming that the device is infected with a virus or has been compromised. The message may include alarming language and instructions to call a phone number immediately.
In other cases, victims receive unsolicited phone calls from individuals claiming to represent well known technology companies. The caller insists that serious issues have been detected on the victim’s device and that immediate action is required to prevent data loss or identity theft.
Once contact is made, scammers attempt to gain remote access to the computer. They may display fake error logs or normal system files and describe them as dangerous threats. This performance is designed to convince the victim that professional intervention is necessary.
After creating fear and confusion, scammers demand payment for unnecessary repairs or software subscriptions. Payment methods often include gift cards, wire transfers, or direct bank payments. Granting remote access can also allow scammers to install malware, steal files, or lock the device until additional payments are made.
Legitimate technology companies do not monitor personal devices or contact users without a request. Popups claiming immediate danger should be closed, not interacted with. If a device issue is suspected, users should seek help through official support channels or trusted local technicians.
Understanding that fear is the main weapon in these scams helps neutralize their effectiveness. Calm verification protects against unnecessary loss.
Image

3. Romance Scams
Romance scams target people seeking emotional connection and companionship. Scammers create fake profiles on dating platforms and social media, often using attractive photos and detailed personal stories. These profiles are designed to appear authentic and relatable.
Once communication begins, scammers invest time in building trust. Conversations may last weeks or months, with frequent messages and expressions of affection. Victims may feel understood, valued, and emotionally connected. This emotional bond is critical to the success of the scam.
Eventually, a crisis is introduced. The scammer may claim to have a medical emergency, business problem, travel issue, or unexpected financial hardship. Requests for money are framed as temporary help or proof of trust. Over time, the requests may increase in frequency and amount.
Scammers often avoid video calls or in person meetings, offering excuses such as work travel, military service, or technical problems. They may also discourage victims from discussing the relationship with friends or family.
Romance scams are particularly damaging because they cause both financial and emotional harm. Victims may feel embarrassed or reluctant to report the crime.
Protection comes from maintaining boundaries and skepticism. Never send money, gifts, or financial information to someone you have not met in person. Be cautious of relationships that escalate quickly or rely heavily on secrecy.
Image
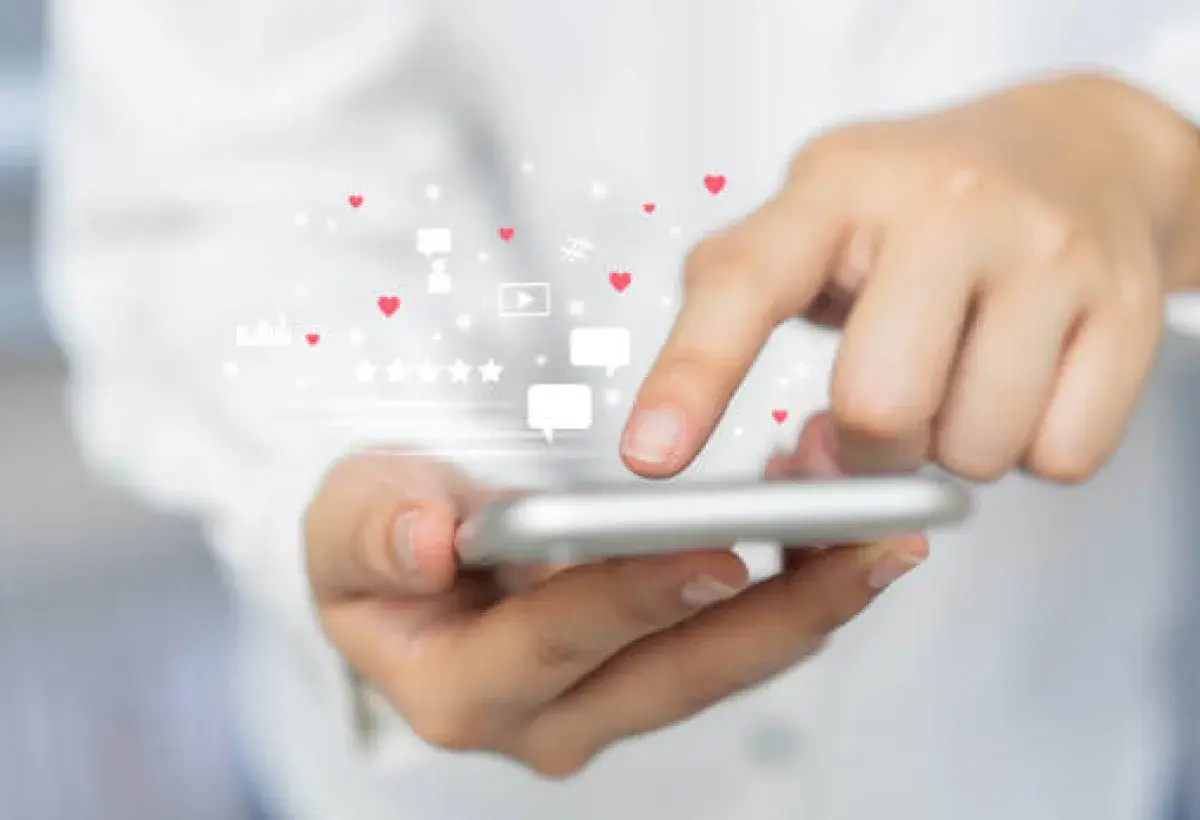
4. Lottery or Prize Scams
Lottery or prize scams rely on excitement and surprise. Victims receive messages claiming they have won a large cash prize, vacation, or giveaway, even though they never entered a contest. These messages may arrive by email, phone call, text message, or traditional mail.
The message often includes official sounding language and branding to appear legitimate. Victims are told that to receive the prize, they must first pay fees, taxes, or processing costs. These payments are typically requested through methods that are difficult to trace or reverse.
Once payment is sent, the prize never arrives. Scammers may continue requesting additional fees or disappear entirely. In some cases, victims are targeted again because they are perceived as willing to engage.
Legitimate lotteries and contests do not require winners to pay upfront fees. Unexpected winnings combined with pressure to act quickly are strong warning signs. Secrecy requests are another red flag.
To stay safe, verify claims independently and remember that prizes are not awarded without participation. When something sounds too good to be true, it usually is.
Image
5. Investment and Crypto Scams
Investment and crypto scams promise high returns with little or no risk. These scams often appear through social media ads, messaging apps, or personal referrals. Scammers may pose as financial experts, successful traders, or friends sharing an exclusive opportunity.
Victims are encouraged to invest quickly before missing out. Fake platforms may show dashboards displaying impressive profits to build confidence. These numbers are fabricated and designed to encourage larger deposits.
When victims attempt to withdraw funds, they encounter delays, fees, or complete account lockouts. Eventually, the platform disappears and contact is lost. Some scams involve pyramid structures where early participants are paid using funds from new victims.
Guaranteed profits are a major red flag. Legitimate investments involve risk and are regulated. Pressure to act quickly and lack of transparency are common indicators of fraud.
Protect yourself by researching opportunities thoroughly, verifying licenses, and consulting trusted financial professionals. Never invest money you cannot afford to lose.
Image

6. Fake Job Offers
Fake job offers are designed to exploit people who are actively searching for employment, remote work, or supplemental income. These scams often appear on job boards, social media platforms, email inboxes, or messaging apps. The offers typically promise high pay, flexible hours, and minimal experience requirements. In many cases, the job sounds unusually easy or too perfect to pass up.
Scammers move quickly to create a sense of legitimacy. They may use company logos, professional language, and fake recruiter profiles. Some victims receive immediate job acceptance without a formal interview or background check. This is often framed as efficiency or urgency, but in reality it is a major warning sign. Legitimate employers take time to evaluate candidates.
Once trust is established, the scam escalates. Victims may be asked to pay upfront fees for training materials, certifications, or work equipment. Others are instructed to provide sensitive personal information such as identification documents, banking details, or tax forms. In more complex cases, victims are used as intermediaries to move stolen funds, unknowingly participating in financial crimes.
Fake checks are another common tactic. Victims receive a check to purchase equipment and are told to send leftover funds back. The check later bounces, leaving the victim responsible for the loss.
To protect yourself, research companies thoroughly, verify job postings on official websites, and be skeptical of offers that require payment or sensitive data early in the process. Legitimate employers do not ask candidates to pay to work.
Image
7. Impersonation Scams
Impersonation scams rely on familiarity and emotional pressure. Scammers pretend to be someone the victim trusts, such as a family member, friend, coworker, or authority figure. These scams often begin with a message claiming an urgent situation that requires immediate financial help.
Common scenarios include a relative who has been arrested, injured, or stranded, or a friend who lost their phone and needs money sent quickly. Some scammers impersonate government officials, law enforcement, or utility companies and threaten legal consequences if payment is not made right away.
The urgency is intentional. Victims are pressured to act before verifying details. Scammers often insist on secrecy, claiming the situation is embarrassing or confidential. Payment requests usually involve wire transfers, gift cards, or digital wallets, which are difficult to trace or reverse.
These scams can be highly convincing because scammers may gather personal details from social media or previous data breaches. They may reference names, relationships, or locations to sound authentic.
The best defense is verification. Pause before responding to urgent requests. Contact the person or organization directly using a known phone number or communication method. Authority figures do not demand immediate payment through unconventional methods.
Image

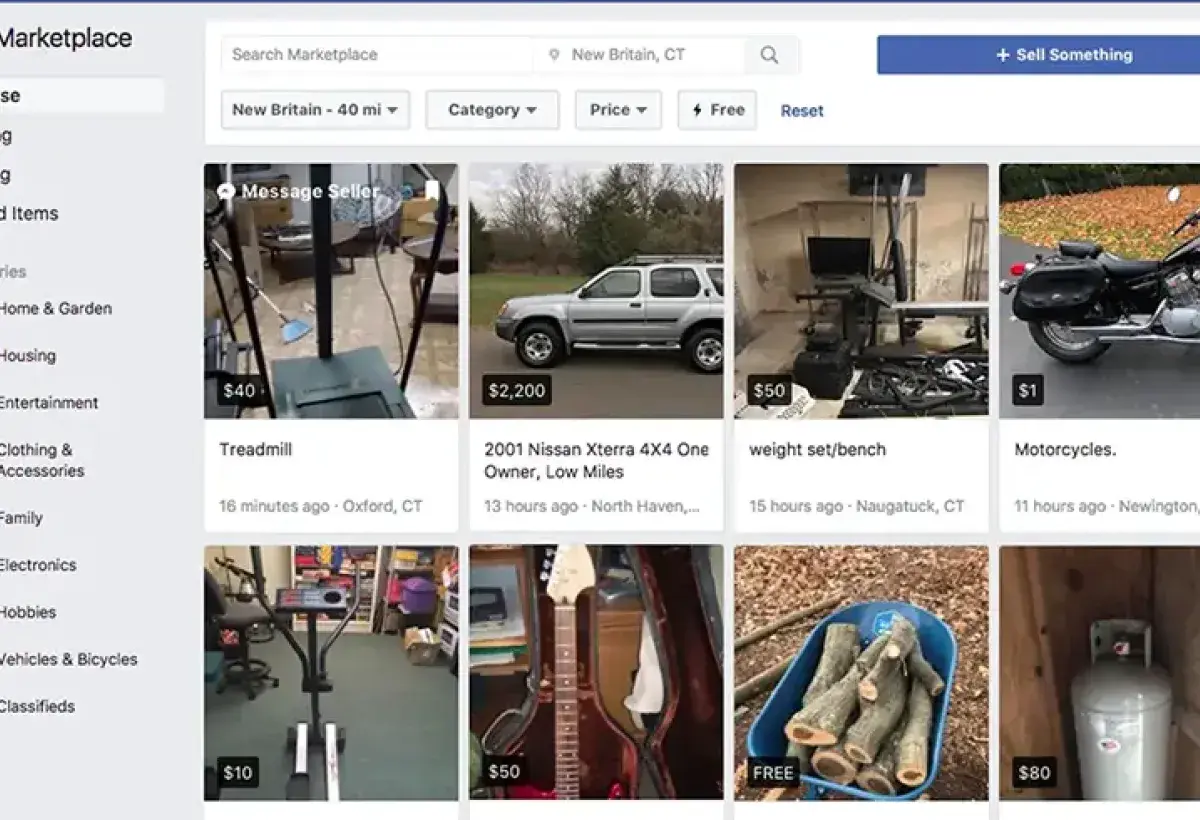
8. Online Marketplace Scams
Online marketplace scams occur on platforms where people buy and sell goods locally or internationally. Scammers take advantage of trust between buyers and sellers by offering deals that appear legitimate and attractive. These scams can affect both sides of a transaction.
Fake sellers often post high demand items at unusually low prices. They may claim urgency, limited availability, or personal reasons for quick sale. Buyers are encouraged to move the conversation off the platform and send payment directly. Once payment is sent, the seller disappears and the item is never delivered.
Fake buyers use different tactics. They may send fraudulent payment confirmations or overpay with stolen funds and request a refund. When the original payment is reversed, the seller loses both the item and the refunded money.
Some scams involve fake shipping confirmations, counterfeit items, or manipulated screenshots to create false proof of legitimacy.
To stay safe, keep communication and payments within the marketplace platform, review seller ratings carefully, and avoid deals that pressure immediate action. Trust built in a rush is often manufactured.
[Image placement cue: Online marketplace listing with suspicious pricing]
Image alt title: Fake marketplace listing designed to lure buyers
Image
9. Charity Scams
Charity scams exploit compassion and generosity, especially during disasters, crises, or holiday seasons. Scammers create fake charities or impersonate real organizations to solicit donations. These appeals often use emotional stories and urgent messaging to encourage immediate giving.
Requests may arrive through email, social media, phone calls, or crowdfunding platforms. Some scammers use names and logos that closely resemble legitimate charities, making it difficult to tell the difference at a glance. Others pose as volunteers collecting donations directly.
Victims believe their money is helping people in need, but donations are instead used for personal gain. Once funds are sent, they are rarely recoverable.
Pressure tactics are a major red flag. Legitimate charities welcome informed donors and provide transparent information about their mission and finances. They do not demand immediate action or discourage verification.
Before donating, research organizations through official websites and independent charity evaluators. Donate directly through trusted channels rather than responding to unsolicited requests.
Image
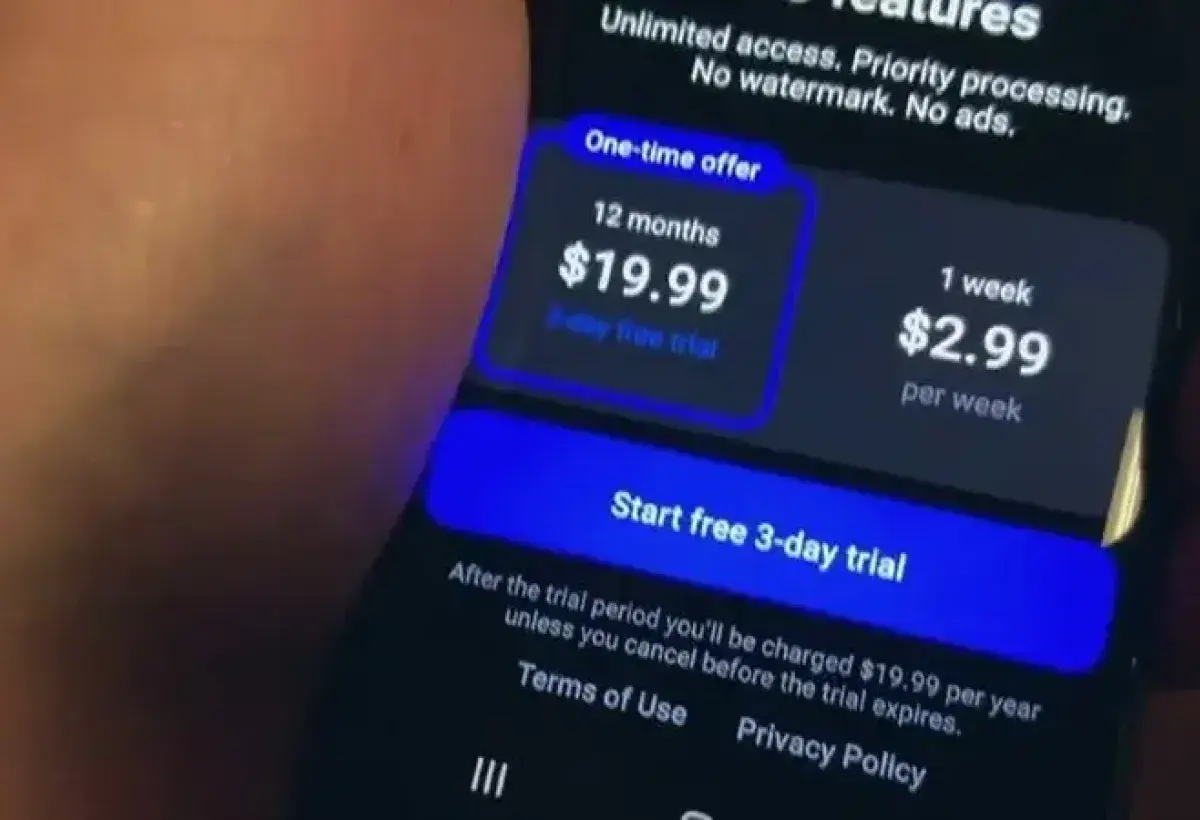
10. Subscription and Free Trial Traps
Subscription and free trial scams are designed to quietly drain money over time. These scams often appear as free offers for streaming services, software, wellness products, or exclusive memberships. While the initial sign up seems harmless, important details are hidden in fine print.
Victims unknowingly agree to recurring charges that begin after a short trial period. Cancelation processes may be intentionally confusing, requiring multiple steps or unavailable customer support. Charges continue even when services are unused.
Some scams make it difficult to identify the source of charges, using vague billing names that do not match the original offer. Others collect payment details and enroll users in multiple subscriptions without clear consent.
To protect yourself, read terms carefully before signing up, avoid using primary payment cards for trials, and monitor bank statements regularly. Set reminders to cancel before trial periods end.
Transparency is key. Legitimate companies clearly disclose pricing and make cancellation straightforward.
Image
Scams thrive on speed, emotion, and distraction. They succeed when people feel rushed, afraid, excited, or overly trusting. While scammers continue to evolve, their core tactics remain predictable once you know what to look for. Awareness and patience are powerful tools that can stop fraud before it starts.
Taking a moment to verify information, question unexpected requests, and consult trusted sources can make a critical difference. Sharing knowledge about common scams helps protect others who may be less informed or more vulnerable. Staying safe is not about fear, but about confidence and control.
By recognizing warning signs and staying alert, you reduce your risk of becoming a victim. Scammers rely on silence and secrecy, but informed individuals weaken their reach. Staying smart and cautious helps create a safer environment for everyone, both online and offline.